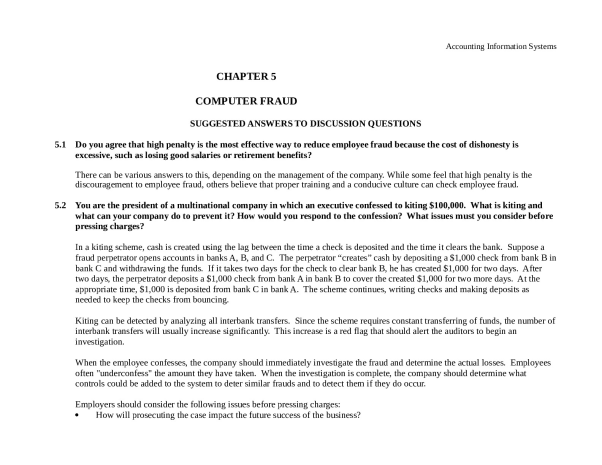
Accounting Information Systems
CHAPTER 5
COMPUTER FRAUD
SUGGESTED ANSWERS TO DISCUSSION QUESTIONS
5.1 Do you agree that high penalty is the most effective way to reduce employee fraud because the cost of dishonesty is
excessive, such as losing good salaries or retirement benefits?
There can be various answers to this, depending on the management of the company. While some feel that high penalty is the
discouragement to employee fraud, others believe that proper training and a conducive culture can check employee fraud.
5.2 You are the president of a multinational company in which an executive confessed to kiting $100,000. What is kiting and
what can your company do to prevent it? How would you respond to the confession? What issues must you consider before
pressing charges?
In a kiting scheme, cash is created using the lag between the time a check is deposited and the time it clears the bank. Suppose a
fraud perpetrator opens accounts in banks A, B, and C. The perpetrator “creates” cash by depositing a $1,000 check from bank B in
bank C and withdrawing the funds. If it takes two days for the check to clear bank B, he has created $1,000 for two days. After
two days, the perpetrator deposits a $1,000 check from bank A in bank B to cover the created $1,000 for two more days. At the
appropriate time, $1,000 is deposited from bank C in bank A. The scheme continues, writing checks and making deposits as
needed to keep the checks from bouncing.
Kiting can be detected by analyzing all interbank transfers. Since the scheme requires constant transferring of funds, the number of
interbank transfers will usually increase significantly. This increase is a red flag that should alert the auditors to begin an
investigation.
When the employee confesses, the company should immediately investigate the fraud and determine the actual losses. Employees
often "underconfess" the amount they have taken. When the investigation is complete, the company should determine what
controls could be added to the system to deter similar frauds and to detect them if they do occur.
Employers should consider the following issues before pressing charges:
How will prosecuting the case impact the future success of the business?
Ch. 5: Computer Fraud
What effect will adverse publicity have upon the company's well being? Can the publicity increase the incidence of fraud by
exposing company weaknesses?
What social responsibility does the company have to press charges?
Does the evidence ensure a conviction?
If charges are not made, what message does that send to other employees?
Will not exposing the crime subject the company to civil liabilities?Accounting Information Systems
5.3 Discuss the following statement by Roswell Steffen, a convicted embezzler: “For every foolproof system, there is a method
for beating it.” Do you believe a completely secure computer system is possible? Explain. If internal controls are less than
100% effective, why should they be employed at all?
The old saying "where there is a will, there is a way" applies to committing fraud and to breaking into a computer system. It is
possible to institute sufficient controls in a system so that it is very difficult to perpetrate the fraud or break into the computer
system, but most experts would agree that it just isn't possible to design a system that is 100% secure from every threat. There is
bound to be someone who will think of a way of breaking into the system that designers did not anticipate and did not control
against.
If there were a way to make a foolproof system, it would be highly likely that it would be too cost prohibitive to employ.
Though internal controls can't eliminate all system threats, controls can:
Reduce threats caused by employee negligence or error. Such threats are often more financially devastating than intentional
acts.
Significantly reduce the opportunities, and therefore the likelihood, that someone can break into the system or commit a
fraud.
5.5 Because improved computer security measures sometimes create a new set of problems—user antagonism, sluggish
response time, and hampered performance—some people believe the most effective computer security is educating users
about good moral conduct. Richard Stallman, a computer activist, believes software licensing is antisocial because it
prohibits the growth of technology by keeping information away from the neighbors. He believes high school and college
students should have unlimited access to computers without security measures so that they can learn constructive and
civilized behavior. He states that a protected system is a puzzle and, because it is human nature to solve puzzles, eliminating
computer security so that there is no temptation to break in would reduce hacking.
Do you agree that software licensing is antisocial? Is ethical teaching the solution to computer security problems? Would
the removal of computer security measures reduce the incidence of computer fraud? Why or why not?
Answers will vary. Students should consider the following conflicting concepts