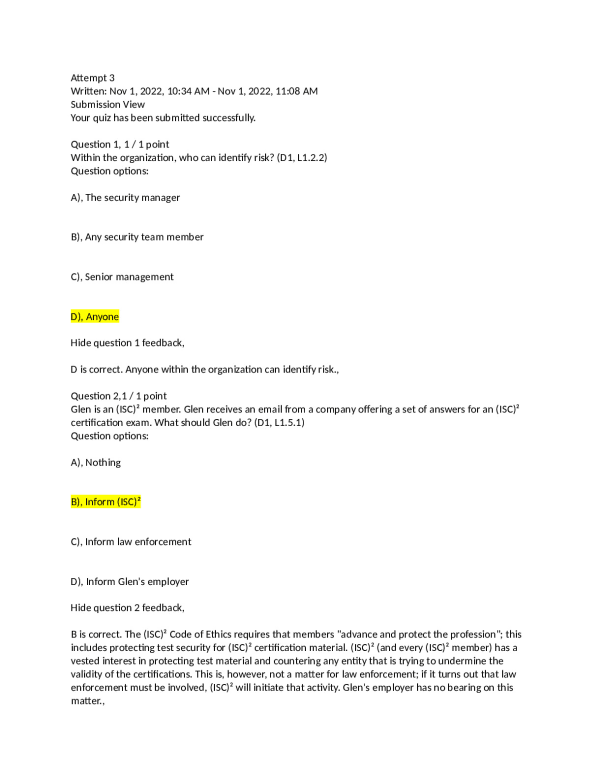
Attempt 3 Written: Nov 1, 2022, 10:34 AM - Nov 1, 2022, 11:08 AM Submission View Your quiz has been submitted successfully. Question 1, 1 / 1 point Within the organization, who can identify risk? (D1, L1.2.2) Question options: A), The security manager B), Any security team member C), Senior management D), Anyone Hide question 1 feedback, D is correct. Anyone within the organization can identify risk., Question 2,1 / 1 point Glen is an (ISC)² member. Glen receives an email from a company offering a set of answers for an (ISC)² certification exam. What should Glen do? (D1, L1.5.1) Question options: A), Nothing B), Inform (ISC)² C), Inform law enforcement D), Inform Glen's employer Hide question 2 feedback, B is correct. The (ISC)² Code of Ethics requires that members "advance and protect the profession"; this includes protecting test security for (ISC)² certification material. (ISC)² (and every (ISC)² member) has a vested interest in protecting test material and countering any entity that is trying to undermine the validity of the certifications. This is, however, not a matter for law enforcement; if it turns out that law enforcement must be involved, (ISC)² will initiate that activity. Glen's employer has no bearing on this matter., Question 3,1 / 1 point Tina is an (ISC)² member and is invited to join an online group of IT security enthusiasts. After attending a few online sessions, Tina learns that some participants in the group are sharing malware with each other, in order to use it against other organizations online. What should Tina do? (D1, L1.5.1) Question options: A), Nothing B), Stop participating in the group C), Report the group to law enforcement D), Report the group to (ISC)² Hide question 3 feedback, B is the best answer. The (ISC)² Code of Ethics requires that members "protect society, the common good, necessary public trust and confidence, and the infrastructure"; this would include a prohibition against disseminating and deploying malware for offensive purposes. However, the Code does not make (ISC)² members into law enforcement officers; there is no requirement to get involved in legal matters beyond the scope of personal responsibility. Tina should stop participating in the group, and perhaps (for Tina's own protection) document when participation started and stopped, but no other action is necessary on Tina's part., Question 4, 1 / 1 point Steve is a security practitioner assigned to come up with a protective measure for ensuring cars don't collide with pedestrians. What is probably the most effective type of control for this task? (D1, L1.3.1) Question options: A), Administrative B), Technical C), Physical D), Nuanced Hide question 4 feedback, C is correct. Physical controls, such as fences, walls, and bollards, will be most likely to ensure cars cannot collide with pedestrians by creating actual barriers between cars and pedestrians. A is incorrect; administrative controls (such as signage and written directions) may be helpful in this situation, but not as helpful as physical controls. B is incorrect because technical controls are typically associated with IT environments and less practical for physical interactions; while helpful, technical controls would most likely not be as useful as physical controls in this situation. D is incorrect because "nuanced" is not a common type of security control, and the word is only used here as a distractor., Question 5, 1 / 1 point A system that collects transactional information and stores it in a record in order to show which users performed which actions is an example of providing ________. (D1, L1.1.1) Question options: A), Non-repudiation B), Multifactor authentication C), Biometrics D), Privacy Hide question 5 feedback, A is correct. Non-repudiation is the concept that users cannot deny they have performed transactions that they did, in fact, conduct. A system that keeps a record of user transactions provides nonrepudiation. B and C are incorrect because nothing in the question referred to authentication at all. D is incorrect because non-repudiation does not support privacy (if anything, non-repudiation, and privacy are oppositional)., Question 6,1 / 1 point The senior leadership of Triffid Corporation decides that the best way to minimize liability for the company is to demonstrate the company's commitment to adopting best practices recognized throughout the industry. Triffid management issues a document that explains that Triffid will follow the best practices published by SANS, an industry body that addresses computer and information security. The Triffid document is a ______, and the SANS documents are ________. (D1, L1.4.2) Question options: A), Law, policy B), Policy, standard C), Policy, law D), Procedure, procedure Hide question 6 feedback, B is the correct answer. The Triffid document is a strategic, internal rule published by senior management; this is a policy. The SANS documents are industry best practices recognized globally; these are standards. A and C are incorrect, because neither document was issued by a governmental body, so they are not laws. D is incorrect because neither document is a detailed set of instructions, so they are not procedures., Question 7, 1 / 1 point Preenka works at an airport. There are red lines painted on the ground next to the runway; Preenka has been instructed that nobody can step or drive across a red line unless they request, and get specific permission from, the control tower. This is an example of a(n)______ control. (D1, L1.3.1) Question options: A), Physical B), Administrative C), Critical D), Technical Hide question 7 feedback, B is correct. The process of requesting and getting permission, and the painted signage, are examples of administrative controls. A is incorrect; while the line is painted on the ground (and the ground is a tangible object), the line does not actually act to prevent or control anything—the line is a symbol and indicator; Preenka could easily walk across the line, if Preenka chose to do so. C is incorrect; "critical" is not a term commonly used to describe a particular type of security control and is used here only as a distractor. D is incorrect; a painted line is not an IT system or part of the IT environment., Question 8, 1 / 1 point For which of the following assets is integrity probably the most important security aspect? (D1, L1.1.1) Question options: A), One frame of a streaming video B), The file that contains passwords used to authenticate users C), The color scheme of a marketing website D), Software that checks the spelling of product descriptions for a retail website Hide question 8 feedback, B is correct. If a password file is modified, the impact to the environment could be significant; there is a possibility that all authorized users could be denied access, or that anyone (including unauthorized users) could be granted access. The integrity of the password file is probably the most crucial of the four options listed. A is incorrect because one frame of an entire film, if modified, probably would have little to no effect whatsoever on the value of the film to the viewer; a film has thousands (or tens of thousands, or millions) of frames. C is incorrect because a change in marketing material, while significant, is not as crucial as the integrity of the password file described in Answer B. D is incorrect because a typo in a product description is not likely to be as important as the integrity of the password file described in Answer B., Question 9, 1 / 1 point In risk management concepts, a(n) _________ is something a security practitioner might need to protect. (D1, L1.2.1) Question options: A), Vulnerability B), Asset C), Threat D), Likelihood Hide question 9 feedback, B is correct. An asset is anything with value, and a security practitioner may need to protect assets. A, C, and D are incorrect because vulnerabilities, threats and likelihood are terms associated with risk concepts, but are not things that a practitioner would protect., Question 10, 1 / 1 point Sophia is visiting Las Vegas and decides to put a bet on a particular number on a roulette wheel. This is an example of _________. (D1, L1.2.2) Question options: A), Acceptance B), Avoidance C), Mitigation



-preview.png)